Sekuro proudly hosted an event with the team at Mills Oakley, bringing Minister Clare O'Neil and business leaders together for an update and a constructive discussion about Australia’s progress to a cyber resilient nation.
On the 18th of May 2023, Sekuro, Mills Oakley and business leaders joined the Minister for Home Affairs and Cyber Security, Clare O’Neil, to discuss Australia’s progress to becoming a cyber resilient nation. The event included an update from the Minister as well as a panel discussion and fireside chat.
During her update, Minister O’Neil made it clear that it is her government’s priority to make Australia the most secure nation by 2030. However, this is only possible through the collaboration of the best thinkers and thought leaders in Australia to uplift cyber resilience and capabilities and take a holistic approach to finding solutions.
The Minister acknowledged how rapidly the cyber security landscape is changing and as a policy space, it has changed more in a year than the time Australia has had a cabinet that stands alone in managing it. Not long after the Labour government was elected, major attacks occurred across large Australian organisations such as Medibank, Optus, and Latitude. These attacks go well beyond these individual organisations and it is pivotal that we get the right information out there to build greater solutions and ensure everyday Australians are aware of how serious these attacks can be.
The Minister shared her commitment to protecting Australians and putting a plan in place for future attacks involving energy systems, health care systems, and critical infrastructure.
Photo Credits: Oskar Lim
The most secure nation by 2030
The Minister’s goal is to make Australia the most secure nation by 2030. Why 2030? By then, the digital landscape will look vastly different to today and the Minister believes cyber will be a bigger and darker problem, with the key influencing factors being:
- IoT– Billions of more devices will be online which will open up the doors to enormous threats and vulnerabilities
- AI – As this continues to grow, the scale of cyber attacks will intensify
- Geopolitical context – The rise of tensions around the world will increasingly play out in the cyber space.
O’Neil’s team is observing is that cyber security is not anyone’s single responsibility. Her team has planned exercises for major sectors, with the financial sector and big banks being first in line, to facilitate conversations and help industries prepare so that they know what to do when incidents inevitably happen. There will be a department set up for significant incident response.
“What we have is a government that is capable of creating a holistic approach,” the Minister says.
The Minister identified five major areas where work needs to be done:
- Help the community protect themselves. What needs to be done to ensure Australians better understand what they need to do to protect themselves and understand the risks? Most cyber attacks are preventable with a basic understanding of cyber security best practices.
- Define the responsibility of big organisations that can afford to make a difference for individuals. The responsibility of cyber security shouldn’t be pushed on individual Australians, who don’t have the same capacity as corporations to invest in security. E.g. big banks, providers of cloud services, Telstra. What do we ask of these companies? What obligations do we set?
- Critical infrastructure needs to be thought through further. How does the government support and help owners and providers of critical infrastructure strengthen their cyber security defence. What needs to be done to set up systems so all levels of government can uplift cyberdefences?
- Strengthen the ecosystem: what can Australia do together? The priority is to improve the quality of our migration program, establish a highly skilled workforce and get cyber security professionals talking to young people to inspire them to join the industry.
- Set the global standard for cyber security. Australian leaders need to engage in global forums to set standards and understand the nation’s obligations to the world as leaders in cyber resilience. Australia can build on efforts to become the partner choice of the region and neighbouring Pacific Islands to provide support and solutions for cyber incidents.
O’Neil ended her opening discussion with one piece of advice for all companies : “LISTEN TO YOUR CISOS.”
The Panel Discussion on the Current State of Australia’s Critical Infrastructure Sector
Following the key updates, the Minister joined a panel moderated by Sekuro’s Chief Information Officer, Karan Khosla, to exchange views and insights on the current state of Australia’s critical infrastructure sector and what it’ll take for Australia to increase our cyber capabilities and become the world leader in cyber security.
The panel included:
David Middleton, Chair, Greater Western Water and VIC Water
Jason Symons, Partner, Head of Cyber Risk and Insurance, Mills Oakley
Shamane Tan, Chief Growth Officer, Sekuro

Photo Credits: Oskar Lim

The leaders exchanged valuable perspectives and insights on various topics around Australia’s critical infrastructure and what it will take to increase our cyber capabilities and become a world leader in cyber security. Some of the key topics discussed included:
- Challenges around innovation
- Is the 2030 target of Australia being the most secure nation realistic?
- What role will cyber insurance play to get to the 2030 target?
- Key governance principles for cyber risk
- Communicating effectively with the board is essential management
- Ransoms and class actions
- Plan from the Government to make collaboration easier
Challenges around innovation
The Minister explained that sovereign capabilities is a core part of her teams’ thinking at the moment, and this includes innovating to strengthen all services from supply chains to critical infrastructure. Shamane added that collaboration is key to managing new innovations and we need to be proactive and forward thinking. While it’s hard to keep up with all the new innovations, partnering with businesses to give funds to support the continued investment in cyber security and fostering a culture of innovation will be helpful.
Is the 2030 target of Australia being the most secure nation realistic?
David Mullen responded that it is great to have a tangible target to work towards. To him, it is important to shift the organisational culture to ensure that people understand the gravity of cyber risks. He’s found that running phishing tests and cyber penetration tests have been effective internal exercises to get people to understand the nature of attacks and how to respond. “We hold sensitive and large volumes of data, so we’re acutely aware of what the leak of that data would mean,” as Board Chair, he reflected on the 1985 water supply hack.
Business leaders and the government must collaborate to bolster the cyber security defenses of Australia. O’Neil explained that the government cannot tackle the 2030 goal alone. Australia can increase its cyber capabilities by working together and taking ownership of the shared responsibility to deal with any challenges. The Minister pointed out that threat sharing is a key initiative the government is working on to ensure the right technologies are in place by 2030 to facilitate the sharing of quality data that will inform approaches to cyber attacks.
Shamane seconds the push for collaboration and believes Australia’s culture of openness is one to take advantage of. Tapping into learning, sharing intel and lessons, and having open conversations will make this vision of being a world leader in cyber resilience possible. After all, every leader aims to achieve favorable business outcomes when implementing cyber strategies.
What role will cyber insurance play to get to the 2030 target?
Jason Symons, who has been in the insurance space for many years, says there is tremendous opportunity for collaboration between cyber insurers/advisers with government and the business industry to share knowledge and information around what’s happening in the cyber threat landscape. Above working with businesses to build onto incident response plans and risk management plans, the insurance industry sees what happens after an attack too. This is all vital information the government and industry can tap into to understand the types of incidents and attacks taking place and the types of litigation or regulatory risks that follow.
Key governance principles for cyber risk management
David explained that it is important for boards to understand risk posture and cyber security strategies. There needs to be continued collaboration with security leaders to educate and upskill directors in cyber security.
Living in an Internet age, attacks are inevitable even if Australia become the cyber safest country in the world by 2030. This is why discussions around cyber attacks and defence, must be balanced out with conversations around incident responses.
At a governance level, it is important that directors are clear on what the risk exposure is when a cyber incident occurs and what the response plan is. Boards must have a sound understanding of what’s required to recover, how to ensure compliance and who’s authorised to make a decision in the most critical moments, for example, when a ransom is demanded. How can CISOs help? Share good data and lay out what the business risks are and what can be done to mitigate those risks.
The Minister agreed on the importance of having these conversations regularly. Living in an Internet age, attacks are inevitable even if Australia becomes the cyber safest country in the world by 2030. This is why discussions around cyber attacks and defence, must be balanced out with conversations around incident responses.
Communicating effectively with the board is essential
David urged CISOs to make cyber risks feel real. Tangible data including the number of malware emails the organisation received vs. the number of malware emails the systems have blocked is an effective way to demonstrate the value of investing in cyber solutions. The board chair also encouraged CISOs to create a link between cyber security strategies to organisational strategies. By speaking to boards in a language they can understand, they will see the benefits of putting cyber security high on the agenda.
Shamane extends this sentiment and recommends that CISOs focus on making sure that boards are updated regularly in ways that are relevant to them and to the business strategy. The connection needs to be strong. Shamane also places emphasis on building hope and not being an alarmist. Balance bad news with positive progress happening in the organisation to improve cyber security and– show that there is light at the end of the tunnel.
“There is a risk in the board’s role when it comes to how they manage cyber security management,” Jason adds. Cyber security is a company wide responsibility and making sure discussions around risk management and response plans are had openly with the wider company instead of just amongst cyber teams is key.
Ransoms and class actions
Jason explains that an organisation can’t be naive to the possibility of cyber attacks and ransoms. There is no blanket answer to the question of whether companies should or shouldn’t pay ransoms, as cyber attacks are complex and motivations vary beyond financial gain. There needs to be efforts to improve legislation, and more collaboration with the government to clearly define exceptions to the rule of not paying ransoms for businesses that might have no choice.
Jason noted that when it comes to learning from data breaches, it’s currently hard to get the data to understand what’s happening. Many businesses involved in recent major data breaches are now facing class actions and it’s important for businesses across Australia to understand how those class actions can be relevant to them, particularly in a time where cyber attacks are deemed inevitable. The key is to understand how current legislations around the breach of privacy, breach of contract, and other disclosure laws relate to data breaches. If a precedent is set by recent class actions following data breaches, organisations must understand how it can potentially impact their business and have plans in place for the possibility.
Plan from the Government to make collaboration easier
The Minister explained that as the government is working on refining the national cyber strategy, finding a solution to make it easier to collaborate and share threat information without causing more harm is high on the agenda. The ideal vision is to create technology that enables the sharing of threat information and data in a seamless way.
The government’s role is to become a trusted aggregator so that businesses can willingly share important information around cyber attacks and threats, while being confident that its privacy and business interests are protected. With this information, the government’s mission is to find a way to send that information back to the industry and experts with an intelligence overlay to work on finding solutions together.
Fireside Chat
The discussion continued in the Fireside Chat with John Mullen, Chair of Telstra which was hosted by Shamane Tan.
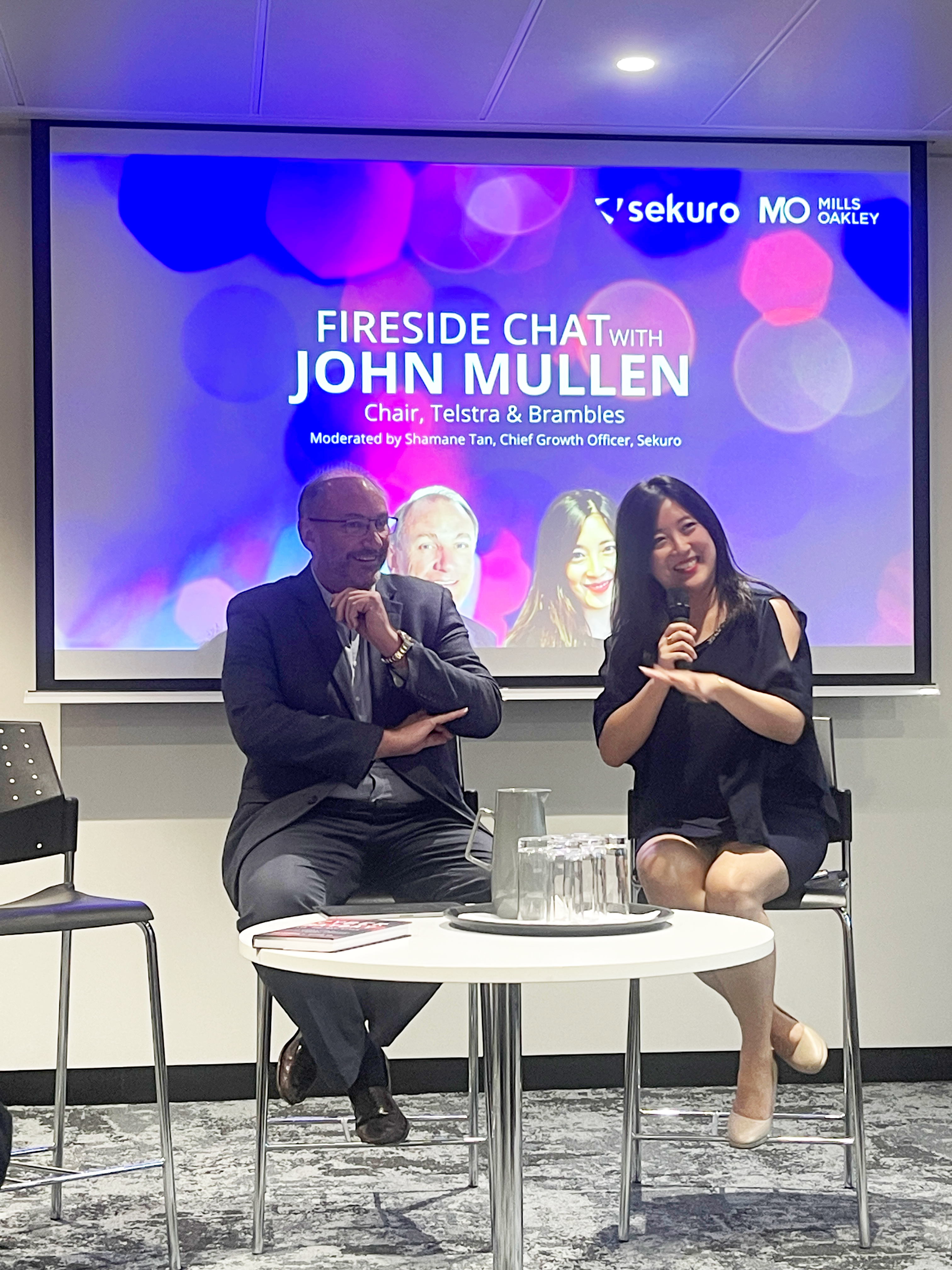
John shared how the magnitude of cyber threats has made him think differently and helped him move from focusing exclusively on prevention to preparedness. He shared some advice for boards: “Every director has an equal responsibility to understand cyber strategies and policies. Cyber is really hard to understand though – as a director, how do you learn that? Persistence is key is the lesson I learnt – even with resistance, keep having those cyber meetings and workshops.”
As for CSOs and CISOs, John shared some advice to help them help their boards. “If your board needs to be persuaded on cyber security, then change your board. It’s 2023 and cyber needs to be a known priority. People’s lives are at risk. Boards and management need to understand you cannot afford to not care about cyber.”
John explained that in order to help boards, information and education is key. He noted that penetration testing has been effective – as it helps boards and leaders understand the gravity of their actions and what can happen if cybercriminals get into organisations.
Every director has an equal responsibility to understand cyber strategies and policies. Cyber is really hard to understand though – as a director, how do you learn that? Persistence is key is the lesson I learnt – even with resistance, keep having those cyber meetings and workshops.
– John Mullen, Chairman of Telstra
As the day came to a close after the industry leaders shared unique perspectives and glimpses into how they’re managing cyber risks within their own organisations, one thing was clear: we have to work together.
Many thanks to all who attended and we look forward to pushing onwards with our shared vision of cyber resiliency in the years to come.

Photo Credits: Oskar Lim