How can companies securely enter into the Cloud world?
In this white paper, gain insights into the benefits offered by Cloud Service Providers (CSP), the key risks and challenges in adopting such services, and lastly, guidelines on addressing an organisation’s security requirements.
By clicking submit, you consent to allow Sekuro to store and process the personal information submitted above to provide you the content requested. For more information on how to unsubscribe, our privacy practices, and how we are committed to protecting and respecting your privacy, please review our Privacy Policy.
Author

Prashant Haldankar
The co-founder and the Chief Information Security Officer (CISO) at Sekuro, a global cyber security and digital transformation company headquartered in Sydney, providing end-to-end cybersecurity and digital resiliency services and solutions. Prashant leads the business resilience function globally with extensive experience establishing and maintaining cyber security visions, strategies and information asset protection frameworks for enterprises.
Cloud Security Assessment
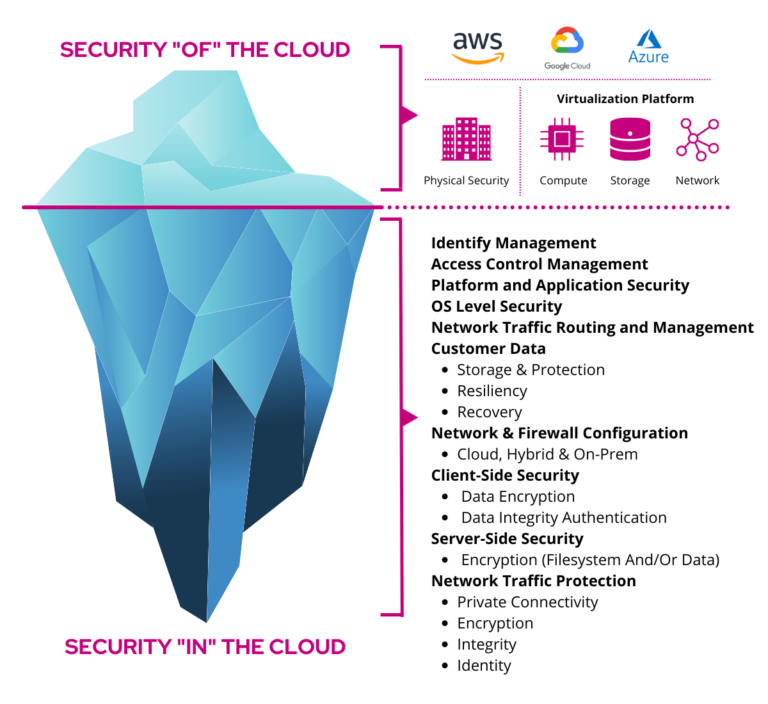
Sekuro’s Cloud Security Assessment service is the ideal first step for any organisation adopting cloud technologies as part of their business strategy. Cloud Service Providers operate on a ‘Shared Security Model’ whereby the lower end of the technology stack is secured, monitored and maintained by the vendor, leaving the upper end of the stack to be secured by the organisation.
Although the responsibility of confidentiality, integrity and availability of data in the cloud is shared between the provider and organisation, the responsibility split is far from even. Using the ‘Iceberg’ analogy demonstrates how much of the responsibility falls onto the organisation.
This can be a daunting task for any organisation to undertake, even those with ready access to skilled cloud security engineers.
Sekuro’s Security Consultants are part of our Technologies and Platforms group, and have extensive experience with Cloud Security good practices and have helped numerous clients secure their cloud environments across multiple vendors. Using industry best-practices and best-of-breed assessment technology, Sekuro is able to harness the power of the cloud using cloud-native functionality to rapid perform security & configuration assessments across thousands of cloud security configurations.
Sekuro’s Cloud Security Assessments provide you with detailed visibility in your cloud security posture and in-depth risk analysis into various components including:
- Identity & Access Management;
- Roles and Policies;
- Enterprise Communications;
- Data Integrity & Confidentiality;
- System Redundancy;
- Workloads & Applications;
- Data Storage;
- Databases;
- Network & Routing; and
- Container, Serverless and FaaS Security.
Sekuro Cloud Security Assessments provide clear, concise, actionable intelligence to business stakeholders about the current state of their cloud security posture and valuable insight on how to protect the organisation in the cloud.
Your Cloud Security Assessment Report includes:
- An executive summary detailing our scope, approach and summary findings and recommendations. This section is aimed at the executive management and contains summarised, non-technical descriptions of cloud security issues alongside a business interpretation of the key business security risks.
- Detailed findings and observations section which includes the detailed assessment findings, the business security risks from identified security issues discovered by the team, as well as recommendations on how best to mitigate these risks.
- Detailed recommendations will be based on industry best practice security recommendations to maintain the confidentiality, integrity and availability of the systems and information assets in the cloud.
